Sleeper Cell Attack Readiness: What Law Enforcement Leaders Must Fix Before the Next Coordinated Attack
The threat is not theoretical. The bigger problem is that too many agencies still train for neat, isolated incidents while real-world attacks are layered, fast, deceptive, and designed to overwhelm weak systems. If your department cannot detect mobilization early, share intelligence quickly, harden soft targets, and respond under chaos, then the label does not matter. You are not ready.
What this article covers
The threat is already here. The readiness gap is the real problem.
Let’s get straight to the point. The real danger is not whether the next attack fits a Hollywood version of a “sleeper cell.” The real danger is whether your agency can identify mobilization behavior, move intelligence fast, protect crowded places, and fight through a coordinated event without breaking down. DHS warned in its June 22, 2025 National Terrorism Advisory System bulletin that the United States was operating in a heightened threat environment tied in part to the Israel-Iran conflict, including concern over cyber activity and possible violence inspired by current events.[1]
That warning should have forced serious agencies to tighten procedures immediately. Instead, many departments still train for clean, controlled scenarios: one suspect, one scene, one channel, one clean timeline. Real attacks do not arrive that way. They may involve vehicles, firearms, explosive devices, diversionary tactics, crowd panic, secondary scenes, and digital coordination. If your people only know how to solve simple training problems, they will struggle when a real event becomes complex in the first two minutes.
The next major failure will not happen because nobody warned us. It will happen because too many agencies confused awareness with readiness.
Stop chasing labels. Start watching behavior.
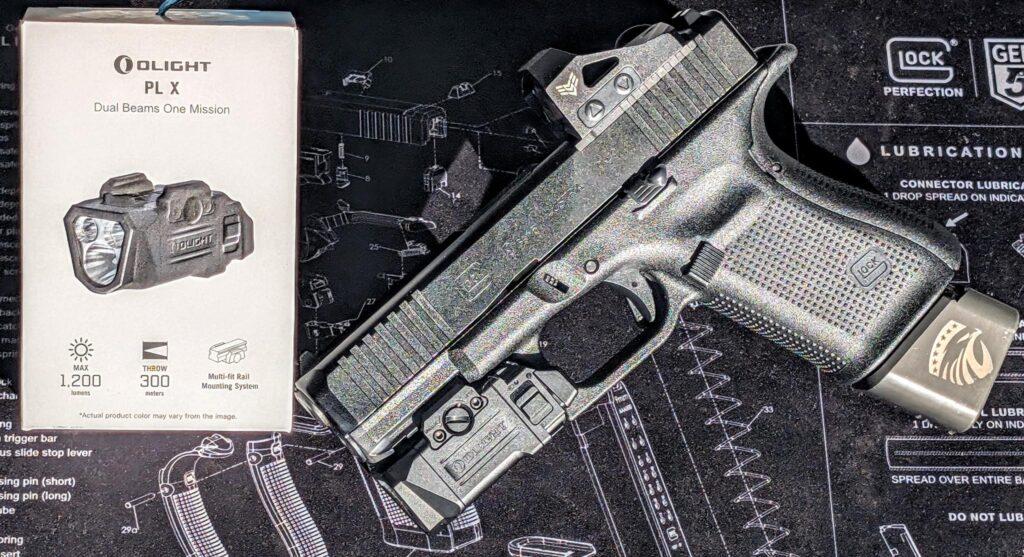
This is where weak agencies make expensive mistakes. Federal guidance does not tell law enforcement to look for caricatures, buzzwords, or stereotypes. The 2025 FBI-NCTC-DHS violent extremism mobilization indicators focus on contextual behavior that may signal movement toward violence. That includes target surveillance, suspicious travel, concealment tactics, suspicious weapons acquisition, attempts to obtain explosive precursors, research into tactics or targets, efforts to gain sensitive access, and steps to build more operational security.[2]
In plain language, stop waiting for somebody to announce the attack. Stop pretending the absence of a manifesto means the absence of a threat. Professional policing means recognizing the preparation cycle before it becomes body counts.
What serious agencies train for
Pattern recognition, lawful documentation, intelligence flow, interagency communication, soft-target planning, response under chaos, and rapid adaptation when a single event turns into multiple scenes.
What unserious agencies rely on
Checklists, weak tabletop exercises, generic “active shooter” blocks, and the false assumption that federal partners will solve the problem before local warning signs ever surface.
Real cases prove the readiness gap is not hypothetical
The Bourbon Street attack in New Orleans on January 1, 2025 was a brutal reminder of what hybrid violence looks like. The FBI stated that the attacker drove a pickup truck into a crowd, exited the vehicle, and fired on law enforcement. Investigators later outlined extensive pre-attack planning and recovered evidence tied to a layered assault model.[3][4]
This was not a clean textbook incident. It was the exact kind of overlapping violence that exposes fragile training systems and weak command assumptions. The lesson is not just about terrorism. The lesson is about complexity. If your agency cannot operate when the event changes shape in real time, then the agency is not prepared.
The warning signs did not stop there. In June 2025, DOJ announced the extradition of Muhammad Shahzeb Khan in connection with an alleged ISIS-inspired plot targeting a Jewish center in Brooklyn, where he allegedly discussed creating “a real offline cell” and carrying out a coordinated assault.[5] In July 2025, SDNY announced charges against a Manhattan man accused of making multiple IEDs intended for use in Manhattan.[6] Then on March 9, 2026, DOJ announced charges against two alleged ISIS supporters accused of attempting to detonate explosive devices in a protest crowd outside Gracie Mansion in New York.[7]
Anyone still pretending cell-style, coordinated, or hybrid attacks are too rare to plan for is not being practical. They are being negligent.
What chiefs, sheriffs, and command staff must fix now
1. Train for layered attacks, not training theater
If your preparedness model is built around one suspect in one building with one predictable response path, it is incomplete. Leaders need realistic scenario-based training that includes vehicles, explosives, multiple scenes, crowd movement, communications overload, casualty management, and intelligence updates under pressure. Real incidents punish simplification.
2. Build behavior-based detection across the entire agency
Counterterrorism is not only an analyst problem. Patrol, dispatch, supervisors, detectives, school resource officers, hospital security partners, and event staff may all see fragments of mobilization. Good agencies teach people how to identify suspicious patterns, document them properly, and move the information without delay.[2]
3. Harden soft targets before they become headlines
Soft targets and crowded places remain attractive because they offer access, symbolism, and impact. CISA’s guidance on securing public gatherings emphasizes planning, staff readiness, reporting pathways, and coordination before the event begins.[8] If your jurisdiction hosts major events without layered planning, unified command integration, suspicious-activity reporting, and route control, you are gambling with public safety.
4. Fix intelligence sharing before the crisis starts
Agencies love to talk about partnership after the attack. Serious leaders build those channels before the attack. Fusion centers, JTTFs, local analysts, neighboring departments, fire-rescue, EMS, venue security, and emergency management need clear pathways for immediate communication. If your intelligence-sharing process only becomes effective after casualties, then it was never effective.
5. Rebuild public vigilance without turning it into profiling
The public often sees behavioral changes first. But lazy messaging creates noise, mistrust, and bad reporting. Federal guidance is clear: protected characteristics and lawful conduct in isolation are not enough.[2] Good agencies teach behavior-based reporting, lawful documentation, and disciplined follow-up.
6. Stop using budget as an excuse
Preparedness funding exists. FEMA’s Homeland Security Grant Program required that at least 35% of HSGP funding be directed to Law Enforcement Terrorism Prevention Activities in FY 2024, and the FY 2025 guidance maintained that requirement.[9][10] In other words, many agencies do not have a money problem. They have a standards problem.
What serious readiness actually looks like
Operational readiness
Realistic force-on-force exercises, multi-site scenario planning, crowd-control contingencies, medical integration, communications fallback plans, and leadership decision-making under compressed timelines.
Intelligence readiness
Suspicious activity reporting procedures, rapid dissemination protocols, local-federal partner integration, event threat assessments, and consistent cross-briefing between patrol, analysts, and command staff.
Community readiness
Behavior-based public reporting campaigns, engagement with houses of worship, schools, private security teams, critical-infrastructure operators, and venue managers long before a high-risk event begins.
Leadership readiness
Command staff that do more than sign policies. Leaders must set standards, demand realistic training, test the system aggressively, and refuse to confuse paperwork with capability.
The Valortec position: awareness is not readiness
Here is the hard truth. Too many agencies still think reading bulletins, attending briefings, and updating binders equals preparedness. It does not. Terrorism readiness is not a talking point. It is not a line item. It is not a public-relations shield. It is an operational capability built through standards, repetition, lawful intelligence work, realistic training, and command-level accountability.
If your officers cannot recognize pre-attack behavior, if your supervisors cannot move information fast, if your city cannot secure crowded venues, and if your response plan falls apart the moment the incident becomes more complex than one suspect in one location, then your agency has work to do.
And that work needs to start now, not after the next headline.
Train for the problem you may actually face
Valortec develops serious training for law enforcement, security professionals, and responsible defenders who understand that response capability, decision-making, intelligence discipline, and force application under pressure are not optional. They are the standard.
Frequently asked questions
What is a sleeper cell attack in practical law enforcement terms?
In operational terms, it refers to a covert or low-visibility individual or small group that remains quiet until activation. From a policing standpoint, the better focus is on observable mobilization behavior, preparation patterns, and coordination indicators rather than dramatic labels.[2]
What should agencies watch for first?
Target surveillance, unusual concealment, suspicious travel, attempts to obtain weapons or explosive precursors for criminal use, tactical research, efforts to gain sensitive access, and emerging operational security behaviors should all be assessed in context and documented lawfully.[2]
What should chiefs and sheriffs prioritize immediately?
Realistic multi-layered scenario training, behavior-based detection across the agency, stronger intelligence-sharing systems, and hardening of public gatherings and other soft targets should move to the top of the list immediately.[8]
Is this only a federal problem?
No. Local officers, dispatchers, analysts, school resource officers, venue security teams, and neighboring agencies often encounter fragments of suspicious behavior first. Federal involvement may come later, but local awareness and action are usually the first line of disruption.
Sources
- DHS National Terrorism Advisory System Bulletin, June 22, 2025:
National Terrorism Advisory System Bulletin
- FBI / NCTC / DHS, 2025 Violent Extremism Mobilization Indicators:
U.S. Violent Extremism Mobilization Indicators
- FBI statement on the New Orleans attack:
FBI Statement on the Attack in New Orleans
- FBI Bourbon Street investigation updates:
Bourbon Street Attack Investigation Updates
- DOJ extradition announcement regarding ISIS-inspired Brooklyn plot:
Pakistani National Extradited to Face Charges
- U.S. Attorney SDNY, Manhattan IED case:
New York Man Charged with Making and Attempting to Use IEDs in Manhattan
- DOJ charges regarding attempted bombing plot outside Gracie Mansion:
U.S. Department of Justice Newsroom
- CISA guidance on securing public gatherings:
Securing Public Gatherings
- FEMA FY 2024 Homeland Security Grant Program guidance:
FY 2024 HSGP Notice of Funding Opportunity
- FEMA Homeland Security Grant Program overview:
Homeland Security Grant Program
This article is for educational and professional awareness purposes. Agencies should align policy, intelligence handling, and operational planning with current law, agency directives, and validated federal guidance.